Automated Forensic Analysis
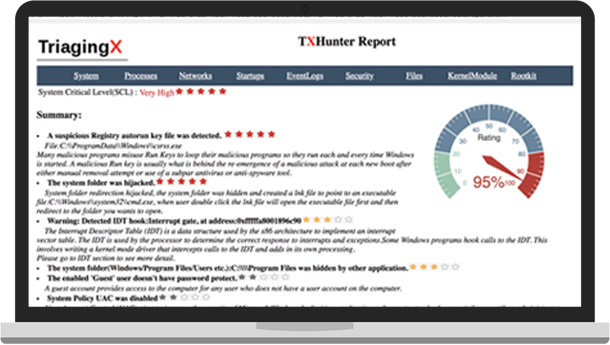
No question or IOC needed, hunting from nothing
Automatically detects all types of threats and the potential risks
Automatical security posture measurement
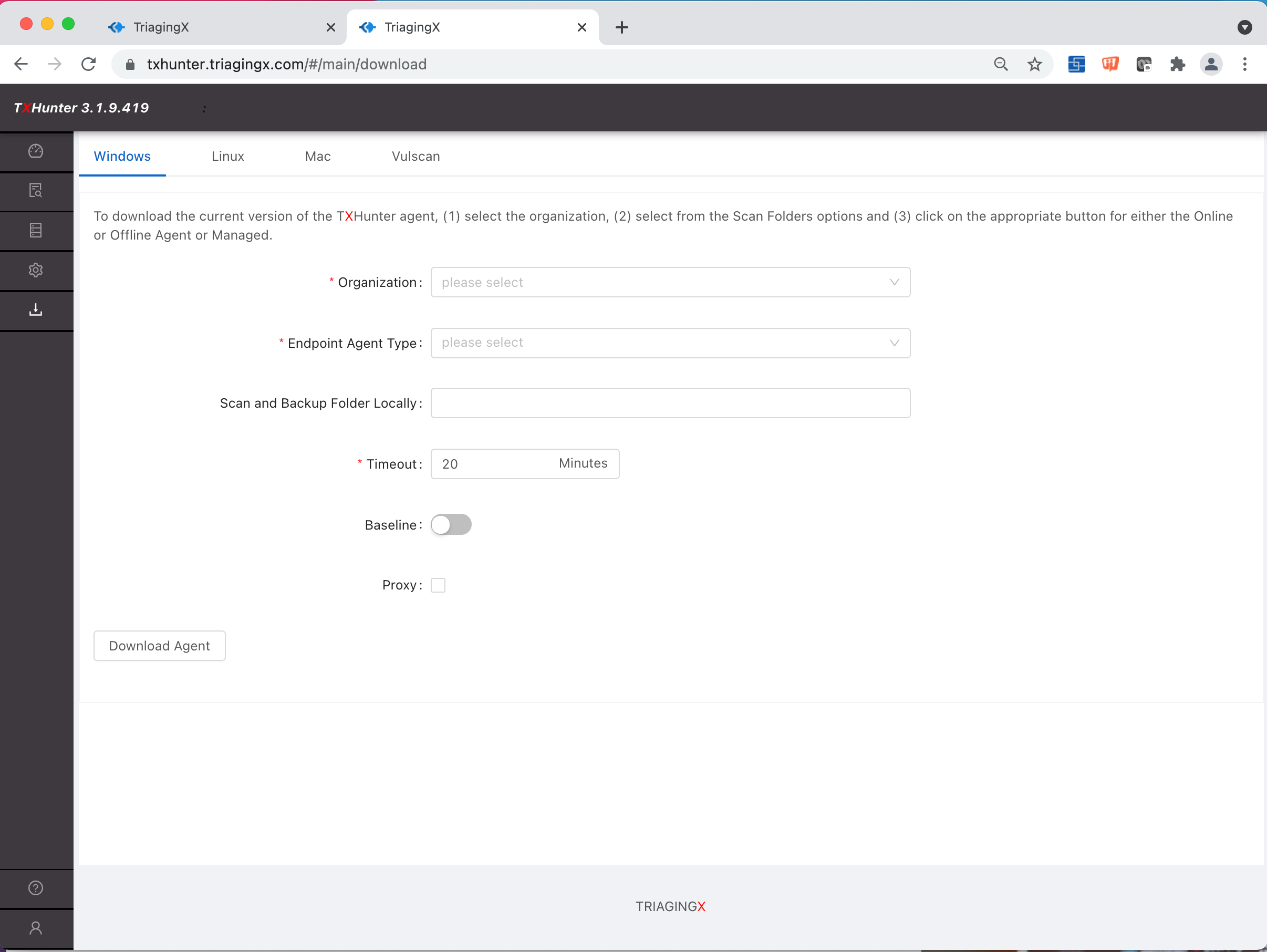
Automatical behavior analysis on suspicious file/URL
Fully automated with FW/IPS/SIEM/EDR alerting systems